Latest
16
Mar

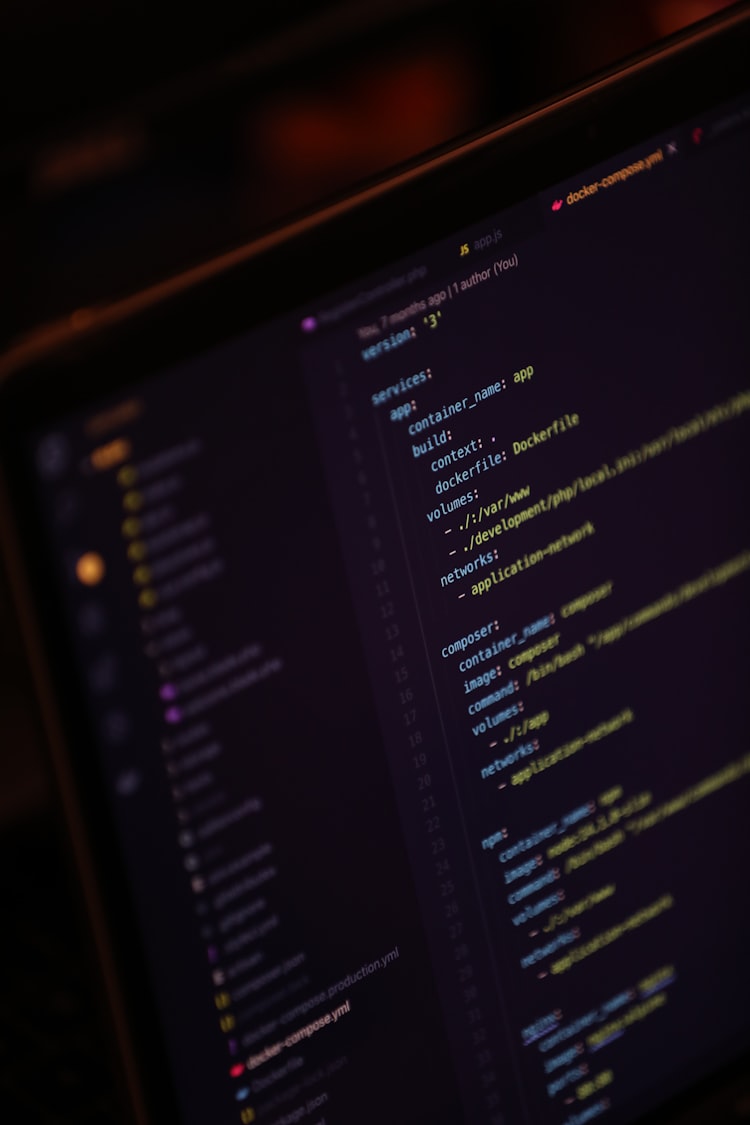
Docker Engine 28
Docker Just Made Containers More Secure—Here’s What You Need to Know
Security in containerized environments has always been
1 min read
30
Jan

Mounting OneDrive on Linux with Rclone
Introduction
If you use OneDrive for cloud storage and want to integrate it seamlessly into your Linux Mint system, Rclone
2 min read
20
Jan

Setting Up Open-WebUI with Ollama: A Comprehensive Guide for CPU and GPU Systems
Are you looking for a PRIVATE flexible and efficient way to run Open-WebUI with Ollama, whether you have a CPU-only
2 min read
06
Jan
The Rise of the AI Generalist: Navigating the Future of Work
The Rise of the AI Generalist: Navigating the Future of Work
Artificial Intelligence (AI) has undergone a remarkable transformation over
5 min read
12
Nov
Who Will Continue Your Family’s Tech Legacy?
For those of us deeply embedded in technology, there’s a unique kind of inheritance that goes beyond the usual
4 min read
05
Oct

Ansible Mini Project Tutorial: Automating Host Updates and User Management
Goals
In this tutorial, I hope you will learn how to create an Ansible project to automate host updates, securely
4 min read
24
Sep

Screen privacy protection - a must have
In our increasingly connected world, many conduct business and handle sensitive information on the go. Whether on the train, at
3 min read
07
Sep

Beware of ‘Quishing’: The Latest QR Code Scam Taking Over the UK and Europe
Over the past few years, QR codes have become a common sight in our daily lives. Whether you’re scanning
4 min read
20
Aug

Unlocking the Power of Windows Package Management with Winget
As an avid user of both Linux and macOS, I've always appreciated the seamless package management systems available
4 min read
30
Jul

Exploring Goofys: A High-Performance Alternative to S3FS-Fuse for Linux
Efficiency and performance are paramount in cloud storage. For Linux users, particularly those who manage large volumes of data, the
2 min read